Most Security Weaknesses Are Only Discovered After an Attack
Many businesses assume their security is strong because tools are in place and systems appear stable. Firewalls are active, antivirus is running, and access controls are configured.
Attackers look for weak entry points, misconfigured systems, and gaps that automated tools often miss. These vulnerabilities do not always appear in reports or alerts. They become visible only when someone actively attempts to exploit them.
Hermetic Networks delivers penetration testing services as an enterprise IT provider that simulates real attack scenarios. Since 2004, we have helped businesses understand how attackers think, where systems are exposed, and what needs to be fixed before it becomes a real incident.
If vulnerabilities are only identified after something breaks, the assessment comes too late.

What Penetration Testing Services Should Reveal
- Exploitable vulnerabilities across systems, networks, and applications.
- Weak access controls and privilege escalation risks.
- Gaps in endpoint security and user authentication.
- Exposure within cloud environments and integrations.
- Risks tied to real-world attack paths, not just theoretical issues.
- Security weaknesses missed by vulnerability assessment tools.
- Clear remediation steps based on actual risk impact.
Why Traditional Security Testing Is Not Enough
Security tools are designed to detect known vulnerabilities, but they do not always show how those vulnerabilities can be exploited in real conditions. A vulnerability may exist, but the real question is whether it can be used to gain access, move laterally, or extract sensitive data.
This is where many businesses fall short. They rely on reports that list issues without understanding the real-world risk behind them. This becomes more complex in environments supported by IT consulting services, where multiple systems interact, and risk is not isolated to a single layer.
Penetration testing services go further by actively attempting to exploit vulnerabilities. This reveals how attackers could move through your environment and what level of damage is actually possible.

A Real-World Approach to Penetration Testing That Exposes Actual Risk
Penetration testing should reflect how attacks happen in real environments, not just how systems are configured.
Hermetic Networks approaches penetration testing services by simulating real attack scenarios across your environment. Instead of just identifying vulnerabilities, we validate how they can be exploited and what impact they create.
As a trusted IT Security Provider, penetration testing is aligned with vulnerability assessments, Microsoft security services, and compliance support to ensure findings translate into meaningful improvements with Managed Cybersecurity Services.
1
Reconnaissance and Target Mapping
The process begins by identifying potential entry points, system exposure, and areas where attackers could gain initial access.
2
Vulnerability Analysis and Exploitation Testing
Identified weaknesses are tested to determine whether they can be exploited and how far access can be extended.
3
Lateral Movement and Access Expansion
Testing simulates how an attacker could move within your environment after gaining access, identifying deeper vulnerabilities.
4
Data Access and Impact Validation
We evaluate whether sensitive data, systems, or controls can be accessed, helping measure the real impact of a breach.
5
Reporting and Remediation Guidance
Findings are translated into clear, prioritized actions that reduce risk and improve security posture.
Penetration Testing Services That Simulate Real Attacks
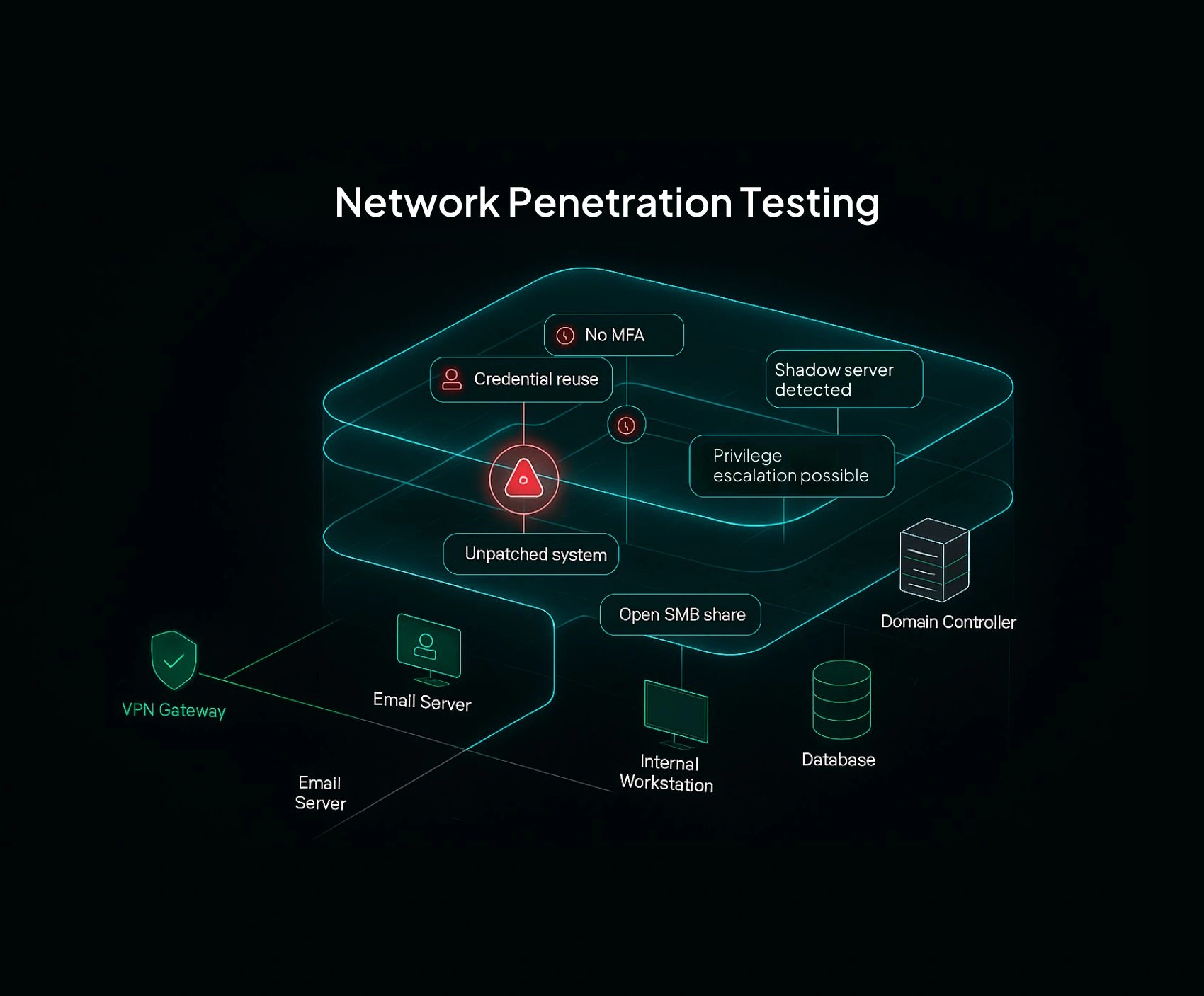
Network Penetration Testing That Identifies External Attack Paths
Networks are often the first target for attackers. Weak configurations or exposed services create entry points that are easy to exploit. We simulate attacks against your network to identify vulnerabilities and validate how they can be used.
Test your network the way attackers would.
- Identify exploitable entry points.
- Validate external access risks.
- Detect misconfigurations in network security.
- Strengthen perimeter defenses.
Web Application Penetration Testing That Protects User Data
Applications are common targets because they interact directly with users and data. Even small vulnerabilities can lead to major exposure. We test applications for real-world exploitability to ensure data remains protected.
Secure applications that drive your business.
- Identify application-level vulnerabilities.
- Test authentication and session controls.
- Detect data exposure risks.
- Strengthen application security posture.


Internal Penetration Testing That Reveals Hidden Risks
Many attacks originate from inside the network, either through compromised credentials or internal access. We simulate internal attack scenarios to identify how far access can be extended once inside.
Understand what happens after the perimeter is breached.
- Test internal system access.
- Identify privilege escalation paths.
- Detect lateral movement opportunities.
- Reduce insider and credential-based risks.
Cloud Penetration Testing That Secures Modern Environments
Cloud systems introduce new risks related to access, configuration, and integration. We perform penetration testing across cloud environments, especially when aligned with Microsoft Azure consulting services and cloud migration services.
Protect cloud environments from real-world threats.
- Identify cloud misconfigurations.
- Test access controls and permissions.
- Validate data exposure risks.
- Strengthen cloud security posture.

The Business Value of Penetration Testing Beyond Security Checks
Penetration testing services are not just about identifying vulnerabilities. They provide real-world validation of how your environment performs under attack conditions. This shifts your security approach from assumption to proof, giving your business clarity, control, and confidence in how risks are managed.
This level of validation becomes more effective when supported through proactive Managed IT Services, where identified risks are continuously monitored and reduced over time.
Validate real-world risk instead of relying on assumptions
Most businesses operate on perceived security rather than tested security. Penetration testing confirms which vulnerabilities can actually be exploited and how far an attacker could go. This level of validation removes uncertainty and allows decisions to be based on real exposure, not theoretical reports.
Strengthen decision-making with actionable security insights
Generic vulnerability data often lacks context. Penetration testing provides clear insight into how risks impact operations, data, and systems. This allows leadership to prioritize investments and improvements based on actual business impact rather than technical noise.
Reduce the likelihood of high-impact security incidents
By identifying exploitable weaknesses early, penetration testing services help prevent incidents that could disrupt operations or compromise sensitive data. Addressing these risks proactively reduces downtime, financial loss, and reputational damage.
Improve system resilience across interconnected environments
Modern IT environments are interconnected, which means one vulnerability can affect multiple systems. Penetration testing reveals how attackers could move across systems, helping strengthen defenses at every layer instead of addressing issues in isolation.
Support compliance with validated security controls
Many compliance requirements expect proof that controls are not only implemented but also effective. Penetration testing services provide that validation, demonstrating that your security measures can withstand real-world attack scenarios.
Enable faster and more confident incident response
Understanding how attacks unfold improves how your team responds to them. Penetration testing provides insight into attack paths, helping your organization react faster and more effectively when security events occur.
Build long-term confidence in your security posture
Security is not just about tools. It is about knowing your environment can withstand real threats. Penetration testing services provide ongoing assurance that your systems are not only protected but tested against the methods attackers actually use.
Why Businesses Struggle Without Penetration Testing
Many businesses rely solely on vulnerability scans or automated tools. While useful, these methods do not show how vulnerabilities behave in real attack scenarios. This creates a false sense of security. Systems appear protected, but the true level of exposure is unknown.
Without penetration testing services, businesses lack insight into how an attacker would actually navigate their environment. This gap becomes critical as systems grow more complex and interconnected.
Why Businesses Choose Hermetic Networks for Penetration Testing
Penetration testing should provide more than technical findings. It should deliver clarity, confidence, and a clear path to reducing real risk.
- Experience simulating real-world attack scenarios: Since 2004, we have helped businesses understand how attackers operate and where systems are truly exposed.
- Focus on exploitable risk, not just identified issues: We validate vulnerabilities to show what can actually be exploited and what impact it creates.
- Actionable insights that drive real improvements: Findings are translated into clear steps that reduce exposure without unnecessary complexity.
- Integration across your full security environment: Testing aligns with IT security assessments, and network infrastructure design and upgrade services.
- Fast response to critical findings: High-risk vulnerabilities are addressed quickly to minimize exposure.
- Ongoing testing that adapts to evolving threats: We continuously refine your security posture as systems and threats change.
The result is a security strategy that is proactive, validated, and built to withstand real-world attacks.
Hear Directly From Our Valued Clients

"The Hermetic Networks team has always been professional, responsive, knowledgeable, and pragmatic in their approach with customers. I highly recommend Jeff and his team to any business that wants a business partner who works to find the best solution for their customers."

Wilson Dickerson
"Hermetic Networks has always been professional and quick to respond to my office's needs. They have come on board with us and offered great solutions, knowledge, and affordability to what our environment requires. I highly recommend Jeff and his team to any business that wants a business partner who works to find the best solution for their customers."

Tyler Carlton
"Amazing service. These guys have the rare ability to combine technical expertise with personal human customer service. Ultimately, the thing everybody hopes for when doing business with someone. Thanks, Jayrd, you went above and beyond."

Todd Peace
Frequently Asked Questions About Penetration Testing Services
Penetration testing services simulate real-world cyber attacks to identify and exploit vulnerabilities, helping businesses understand their true security risk.
