Most Security Gaps Exist Long Before They Are Exploited
A patch is missing. A permission is left open. A system is updated without proper validation.
Individually, these issues may seem minor. Together, they create entry points that attackers actively look for. Many businesses assume their environment is secure because nothing has gone wrong yet. The reality is that vulnerabilities often remain hidden until they are exploited.
Hermetic Networks delivers vulnerability assessment services as a managed security provider that brings visibility into these risks. Since 2004, we have helped businesses uncover weaknesses, prioritize fixes, and strengthen their overall security posture before incidents occur.
If vulnerabilities are not being actively identified, they are accumulating.

What a Proper Vulnerability Assessment Should Reveal
- Hidden weaknesses across systems, applications, and networks.
- Outdated software, patches, and configurations that increase risk.
- Misconfigured access controls and exposed entry points.
- Gaps in endpoint, cloud, and infrastructure security.
- Risks tied to user permissions and identity management.
- Areas where compliance requirements are not being met.
- Prioritized actions to reduce exposure quickly.
Why Vulnerabilities Are Often Missed Inside Businesses
Most vulnerabilities are not missed because tools are absent. They are missed because they are not actively managed. Security tools generate alerts, but those alerts are not reviewed consistently. Systems are deployed securely but not maintained over time. Changes are made without reassessing risk.
Internal teams are often focused on keeping systems running, not continuously evaluating where they are exposed. This becomes more complex in environments supported by network management services, where multiple systems and dependencies evolve simultaneously.
Vulnerability assessment services close that gap by providing structured visibility into your environment.


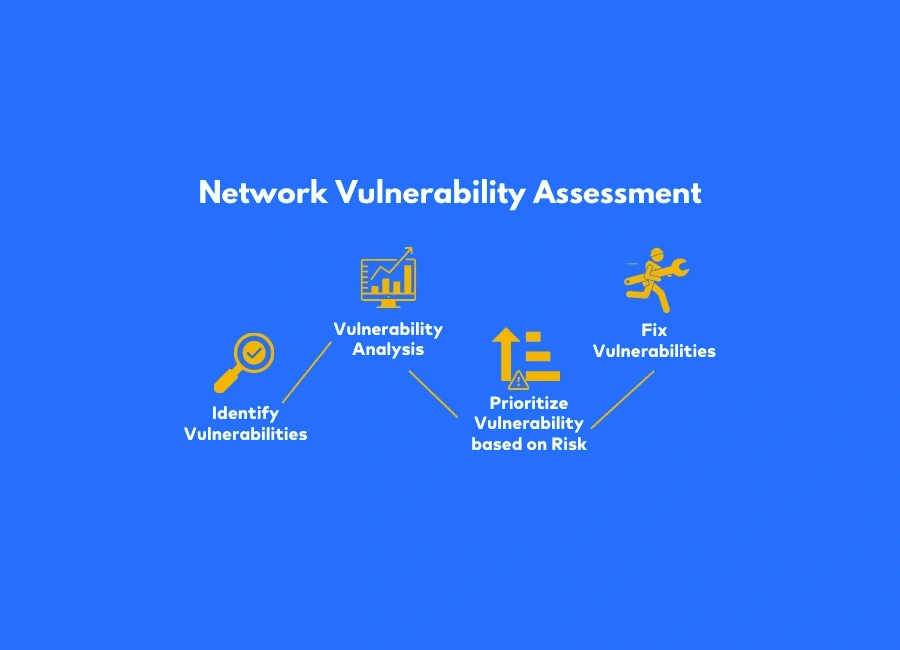
A Structured Approach to Vulnerability Assessments That Reduces Risk
A vulnerability assessment should not just identify issues. It should provide a clear path to reducing risk.
Hermetic Networks delivers vulnerability assessment services by combining technical analysis with practical recommendations. We evaluate your environment across systems, networks, and applications to identify where exposure exists and how it can be reduced.
As a security-focused IT support provider, assessments are aligned with your broader environment, including cybersecurity services, Microsoft 365 Support, and compliance support, ensuring findings are actionable and integrated.
How Vulnerability Assessments Improve Daily Operations
Vulnerability assessment services do more than identify risks. They strengthen how your business operates by bringing clarity, improving system reliability, and reducing uncertainty across your entire environment.
This level of consistency becomes easier to maintain when supported through IT management services, where monitoring, evaluation, and response are continuously aligned with evolving threats.
1
Risks are identified before they turn into disruptions
Vulnerabilities are uncovered early, before they evolve into larger incidents that impact multiple systems or teams. This proactive visibility allows your business to act ahead of threats instead of reacting under pressure.
2
Compliance and audit readiness improve naturally
Regular assessments create ongoing alignment with compliance requirements. Instead of preparing reactively for audits, your environment stays continuously ready with clear documentation and structured controls.
3
Systems perform more consistently under daily workloads
Addressing vulnerabilities improves system stability by eliminating weak points that cause slowdowns, unexpected errors, or outages. This leads to smoother operations and fewer interruptions across critical business processes.
4
Internal teams work with clear priorities instead of guesswork
Structured reporting highlights the most critical vulnerabilities based on real business impact. Instead of chasing scattered issues, your team focuses on what actually reduces risk and improves performance.
5
Cross-system visibility improves coordination
Understanding how vulnerabilities exist across systems, users, and integrations allows teams to manage dependencies more effectively and reduce hidden risks that are often overlooked.
6
IT resources are used more efficiently
With fewer unexpected issues and better visibility, internal teams spend less time troubleshooting and more time improving systems, optimizing performance, and supporting business growth.
7
Security becomes part of operational planning
Vulnerability insights are no longer isolated to IT. They support broader decision-making, helping leadership align security with infrastructure planning, growth initiatives, and technology investments.
Vulnerability Assessment Services That Strengthen Your Security
Network Vulnerability Assessments That Identify Entry Points
Networks often contain hidden access points that attackers can exploit. Without proper visibility, these risks remain undetected. We perform network vulnerability assessments to identify weaknesses across your infrastructure and reduce exposure.
Protect your network from unauthorized access.
- Identify open ports and misconfigurations.
- Detect outdated network components.
- Analyze access points and vulnerabilities.
- Improve overall network security posture.
System Vulnerability Assessments That Reduce Exposure
Operating systems and applications frequently contain vulnerabilities that require ongoing review. We assess systems to ensure they are updated, configured correctly, and protected against known threats.
Keep your systems secure and up to date.
- Identify missing patches and updates.
- Detect configuration weaknesses.
- Reduce system-level vulnerabilities.
- Improve overall system stability.


Cloud Vulnerability Assessments That Improve Visibility
Cloud environments expand quickly, often without consistent oversight. This creates gaps that are difficult to detect without structured analysis. We assess cloud environments to ensure security controls are properly configured and maintained.
This becomes critical in environments supported by Microsoft Azure consulting services, where configuration accuracy directly impacts security and performance.
Maintain visibility and control across your cloud environment.
- Identify cloud misconfigurations.
- Evaluate access and permissions.
- Detect exposure across cloud services.
- Improve cloud security posture.
Application Vulnerability Assessments That Protect Data
Applications are common targets for attackers because they handle sensitive data and user access. We evaluate applications to identify vulnerabilities that could be exploited.
This is especially important in environments supported by IT security assessments, where application-layer risks directly affect overall system integrity.
Protect applications that support your business operations.
- Identify security flaws in applications.
- Detect vulnerabilities in data handling.
- Improve application security controls.
- Reduce risk of exploitation.

Why Businesses Struggle Without Regular Vulnerability Assessments
Many businesses rely on one-time security reviews or assume their environment remains secure after initial setup. The problem is that environments change constantly. New systems are added. Configurations are updated. Threats evolve.
Internal teams often lack the time or tools to continuously evaluate vulnerabilities, which leads to gaps that grow over time. Vulnerability assessment services provide the structure needed to keep security aligned with change.
Why Businesses Choose Hermetic Networks for Vulnerability Assessments
Hermetic Networks delivers vulnerability assessment services as part of a broader operational strategy that connects with managed IT services and IT consulting services, ensuring your security posture is not isolated but aligned with how your business runs every day.
- Experience that reflects real business environments: Since 2004, we have helped organizations identify vulnerabilities that directly impact operations, not just theoretical risks.
- Clear prioritization based on business impact: We focus on what actually matters, ensuring critical vulnerabilities are addressed first to reduce real exposure.
- Actionable insights instead of complex reports: Findings are translated into clear steps your team can implement without confusion or unnecessary complexity.
- Integration across your full IT environment: Assessments connect with Microsoft security services, while also aligning with structured backup and disaster recovery services to ensure resilience after vulnerabilities are addressed.
- Fast response to reduce exposure quickly: Critical vulnerabilities are addressed without delay, minimizing the window of risk across your environment.
- Ongoing assessment that evolves with your business: Your systems change over time, and so do risks. We continuously evaluate and adapt your security posture accordingly.
Working with Hermetic Networks means your vulnerability assessments are not just periodic checks. We become part of a structured approach that strengthens your systems, supports your operations, and ensures your business is always prepared for what comes next.
Built on Trust, Proven by Our Clients

"The Hermetic Networks team has always been professional, responsive, knowledgeable, and pragmatic in their approach with customers. I highly recommend Jeff and his team to any business that wants a business partner who works to find the best solution for their customers."

Wilson Dickerson
"Hermetic Networks has always been professional and quick to respond to my office's needs. They have come on board with us and offered great solutions, knowledge, and affordability to what our environment requires. I highly recommend Jeff and his team to any business that wants a business partner who works to find the best solution for their customers."

Tyler Carlton
"Amazing service. These guys have the rare ability to combine technical expertise with personal human customer service. Ultimately, the thing everybody hopes for when doing business with someone. Thanks, Jayrd, you went above and beyond."

Todd Peace
Frequently Asked Questions About Vulnerability Assessment Services
A vulnerability assessment identifies security weaknesses across systems, networks, and applications so they can be addressed before being exploited.
