Hot off the presses.
Your guide to the latest in business technology trends.
Is Your Office Quietly Leaking Data?
As August rolls in and summer starts to wind down, it’s the perfect time to get back into a steady routine. That includes refreshing the habits that keep your digital workspace safe. The truth is that cybersecurity isn’t just about…
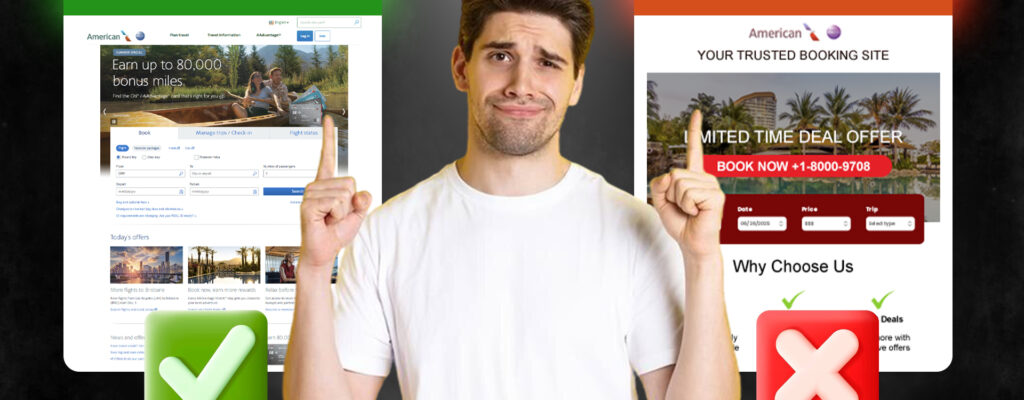
Read More about Is Your Office Quietly Leaking Data?The One Click That Could Ruin Your Vacation
Just because summer is winding down doesn’t mean the travel risks are. Whether you’re squeezing in one last vacation or planning a Labor Day escape, it’s good to stay alert. Cybercriminals are always looking for ways to exploit unsuspecting travelers,…
Read More about The One Click That Could Ruin Your VacationProtecting Your Personal Devices: Cybersecurity Tips for Home and Beyond
Your phone is more than a phone. It is a wallet, a filing cabinet, a work desk, and a personal vault — and hackers know it. The same goes for laptops and tablets, which store everything from financial records to…
Read More about Protecting Your Personal Devices: Cybersecurity Tips for Home and BeyondCybersecurity Horror Stories: Real-Life Attacks That Could Have Been Prevented
Tales of Cyber Disasters In the digital age, cyberattacks are becoming more frequent, sophisticated, and devastating. These horror stories often stem from simple mistakes or overlooked vulnerabilities, leading to severe financial and reputational damage. Whether it’s ransomware paralyzing an organization…
Read More about Cybersecurity Horror Stories: Real-Life Attacks That Could Have Been PreventedTrick or Treat: How Hackers Use Social Engineering to Gain Access
The Deceptive World of Social Engineering Social engineering attacks are some of the most effective tricks used by cybercriminals. By manipulating human emotions like trust, urgency, or fear, hackers deceive individuals into giving up confidential information or access to secure…
Read More about Trick or Treat: How Hackers Use Social Engineering to Gain AccessDesktop Support for Richmond Businesses
Hermetic Networks offers comprehensive desktop support tailored for Richmond businesses. We simplify your IT experience, eliminating the need to juggle multiple vendor contacts. From Microsoft products to QuickBooks and specialized software, our experts are your dedicated IT department, ensuring seamless operations and security.
Read More about Desktop Support for Richmond BusinessesEDR and MDR: A Comprehensive Guide
In the evolving landscape of cyber threats, EDR and MDR stand out as pivotal cybersecurity solutions. Dive into the intricacies of Endpoint Detection and Response (EDR) and Managed Detection and Response (MDR), understanding their unique features and how they fortify businesses against cyberattacks.
Read More about EDR and MDR: A Comprehensive GuideConditional Access: Strengthening Your Security Posture
In today’s rapidly evolving digital landscape, small and medium-sized businesses (SMBs) face many cybersecurity threats. As they rely more heavily on cloud services and remote work, protecting their valuable data has become increasingly critical. As a Managed Services Provider (MSP),…
Read More about Conditional Access: Strengthening Your Security PostureVulnerability Management: 6 Steps to Protect Your Business
In today’s business environment, cybersecurity is more important than ever before. Unfortunately, vulnerabilities are a constant side effect of continual innovation. When software companies push new updates, there are often weaknesses in the code that hackers can exploit. Software developers…
Read More about Vulnerability Management: 6 Steps to Protect Your BusinessMFA and You: Protecting Your Business From Exploits
Protecting sensitive information and corporate accounts is a top priority in the modern business landscape. Companies must take the necessary precautions to secure their online presence with the increasing dependence on technology and the growing threat of cyber attacks. One…
Read More about MFA and You: Protecting Your Business From ExploitsRecent Posts
How can we help?
Whether you need immediate help with an IT issue or want to discuss your long-term IT strategy, our team is here to help.
Call us at (804) 544-1048 or complete the form below and we'll help in any way we can.
"*" indicates required fields